Personal Data Protection Law (KVKK) measures | Personal Data Protection Lawyer | Izmir Lawyer | Izmir Law Firm
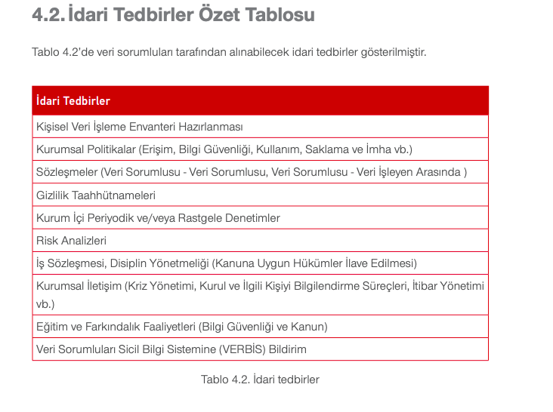
Personal Data Protection Law Article 12 requires data controllers to take administrative and technical measures to ensure an appropriate level of security. So, what measures must be taken under the Personal Data Protection Law (KVKK)?
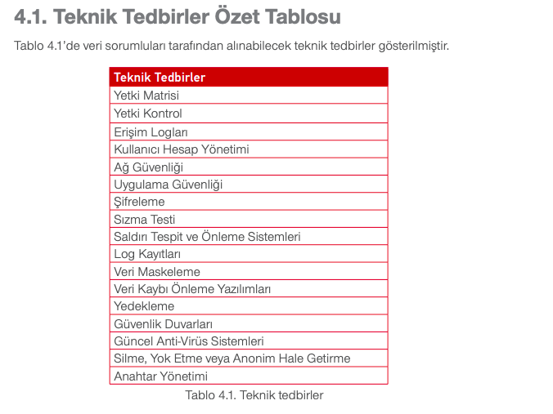
- Network and application securities are provided.
- Closed system network is used for personal data transfers via network.
- Key management is implemented.
- Security measures are implemented within the scope of the procurement, development, and maintenance of information technology systems.
- The security of personal data stored in the cloud is ensured.
- Disciplinary regulations exist for employees that include data security provisions.
- Data security training and awareness programs are conducted periodically for employees.
- An authorization matrix has been created for employees.
- Access logs are kept regularly.
- Corporate policies have been developed and implemented regarding access, information security, usage, storage, and disposal.
- When necessary, data masking measures are applied.
- Confidentiality agreements are being made.
- Employees who have a job change or leave their job are removed from their authority in this area.
- Current anti-virus systems are used.
- Firewalls are used.
- The signed agreements include data security provisions.
- Extra security measures are taken for personal data transmitted via paper, and the relevant documents are sent in a classified document format.
- Personal data security policies and procedures have been established.
- Personal data security issues are reported promptly.
- Personal data security is being monitored.
- Necessary security measures are taken for entering and exiting physical environments containing personal data.
- Physical environments containing personal data are secured against external risks (fire, flood, etc.).
- The security of environments containing personal data is ensured.
- Personal data is minimized as much as possible.
- Personal data are backed up and the security of backed up personal data is also ensured.
- User account management and authorization control system is applied and their follow-up is also performed.
- Internal periodic and/or random audits are conducted and commissioned.
- Log records are kept without user intervention.
- Current risks and threats have been identified.
- Protocols and procedures for the security of sensitive personal data have been established and are being implemented.
- If sensitive personal data is to be sent via email, it must be sent encrypted and using a registered electronic mail (KEP) or corporate email account.
- For sensitive personal data, secure encryption/cryptographic keys are used and managed by different units.
- Intrusion detection and prevention systems are used.
- Penetration test is applied.
- Cyber security measures have been taken and their implementation is constantly monitored.
- Encryption is done.
- Personal data transferred via portable memory, CD, or DVD is encrypted.
- Data processing service providers are subject to periodic audits regarding data security.
- Data processing service providers are being made aware of data security issues.
- Data loss prevention software is used.
To receive advice on this matter, please contact us. Contact page.
For our other articles we have prepared under the Personal Data Protection Law;
- What is KVKK?
- What is Personal Data?
- What are the basic concepts of the Personal Data Protection Law??
- What are the fundamental principles of the Personal Data Protection Law?
- What is a Privacy Notice? What should it include?
- What is a Personal Data Inventory?
- What are the differences between the Personal Data Inventory and the Data Controllers Registry?
- How is the annual number of employees calculated for KVKK (Personal Data Protection Law) registration purposes?
- How should the total financial balance be calculated in relation to the Personal Data Protection Law (KVKK) registration?
- What should a Personal Data Inventory include?
- What are the categories of personal data?
- What are the reasons for processing personal data listed in the Data Controllers Registry?
- What security measures are stipulated in the Data Controllers Registry?
- What should be considered when specifying deadlines in the Data Controllers Registry?
- Exemption from VERBİS Registration
- Legitimate Interest & Balance Test
- WhatsApp Update & Data Security
- Personal Data Protection Law Sanctions
- What is the Right to Be Forgotten?
- Personal Data Protection Law Administrative Fines 2023
- What is GDPR?
- What is DPO? Who are they?
Address: Nergis Neighborhood, Girne Boulevard No: 83, Floor 2, Apartment 2, Karşıyaka, İzmir
E-mail: info@efeshukuk.com
Phone: +90 534 415 52 56
